Business Continuity Plan
& Disaster Recovery Policy
IIP Group Holdings, LLC | May 11, 2026
Table of Contents
1. Introduction
The Business Continuity Plan (BCP) for IIP Group Holdings, Inc., and its subsidiaries (IIP) is designed to ensure that essential functions and operations can continue during and after a disruptive event. This plan provides a framework for responding to and recovering from incidents that may impact business activities. Its goal is to minimize disruption, protect company assets, and maintain stakeholder confidence by outlining clear procedures, responsibilities, and resources required for effective business continuity.
The primary objectives of this plan are to:
Minimize the impact of disruptions on business operations.
Ensure the safety and well-being of employees.
Protect and preserve company assets, including data and infrastructure.
Maintain customer service and stakeholder confidence.
Facilitate a structured and efficient recovery process.
2. Purpose
The purpose of this Business Continuity Plan (BCP) is to ensure that the IIP companies can maintain essential functions during and after a disruptive event. This plan outlines the strategies, procedures, and responsibilities necessary to prepare for, respond to, and recover from incidents that could impact business operations.
3. Scope
The scope of this document includes all users who have access to company-owned or company-provided computers or require access to the corporate network and systems.
This policy and plan apply to employees and guests, contractors, and anyone needing access to the corporate systems to continuously serve our customers. The scope of this plan includes business continuity, disaster recovery, escalation of war, employee safety and its potential impact on business operations.
4. Roles and Responsibilities
BCP Team
BCP Coordinator: Oversees the execution of the BCP and communication.
IT Director: Manages IT recovery and data protection.
Facilities Manager: Coordinates facility-related recovery efforts.
HR Manager: Handles employee communication and support.
Responsibilities
Each team member is responsible for specific recovery tasks as outlined in the plan. Regular training and drills will ensure familiarity with roles.
Preparing for IT Business Continuity Planning (BCP)
For an IT Business Continuity Planning process to be successful, its contribution to overall preparedness efforts must be clear. It must be prioritized by leadership and receive dedicated financial and human resources to ensure operational resilience in case of IT disruptions.
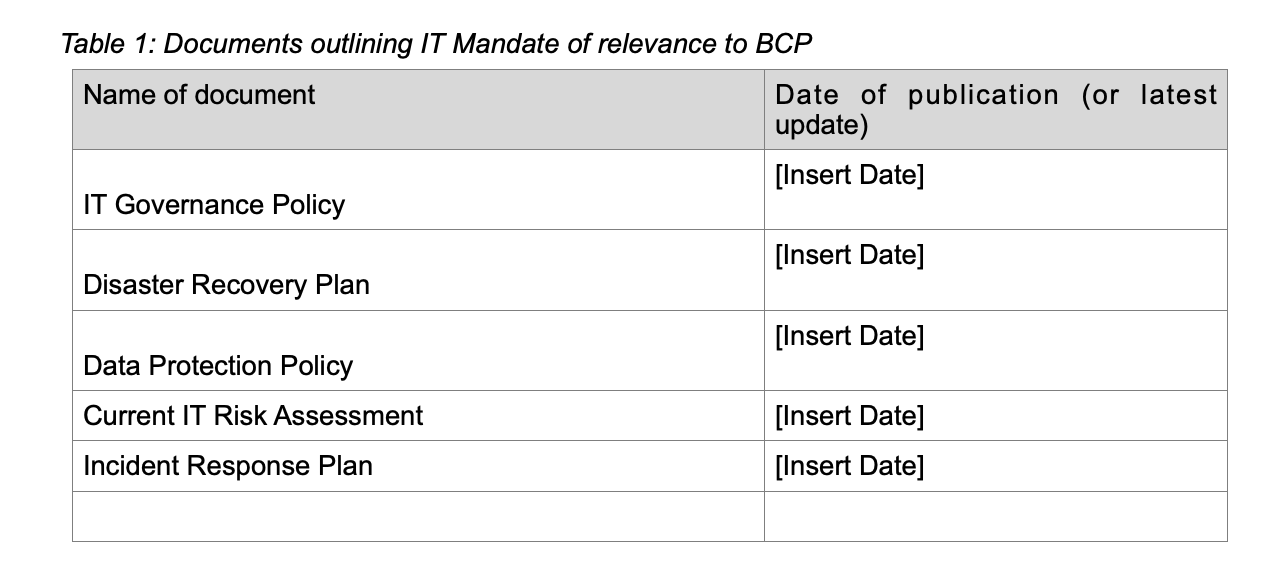
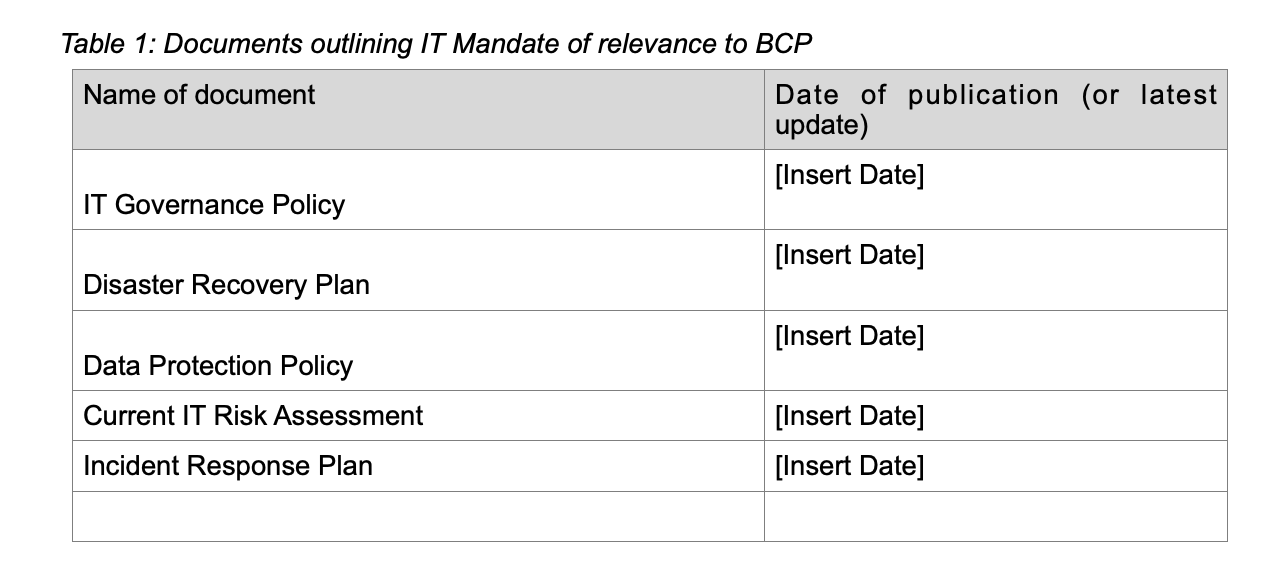
Senior Leadership Mandate:
The IT Business Continuity Plan complements other organizational continuity efforts and ensures that the IT infrastructure, systems, and services remain functional during and after a disruptive event. These commitments and complementary preparedness efforts are outlined in the following organizational documents:
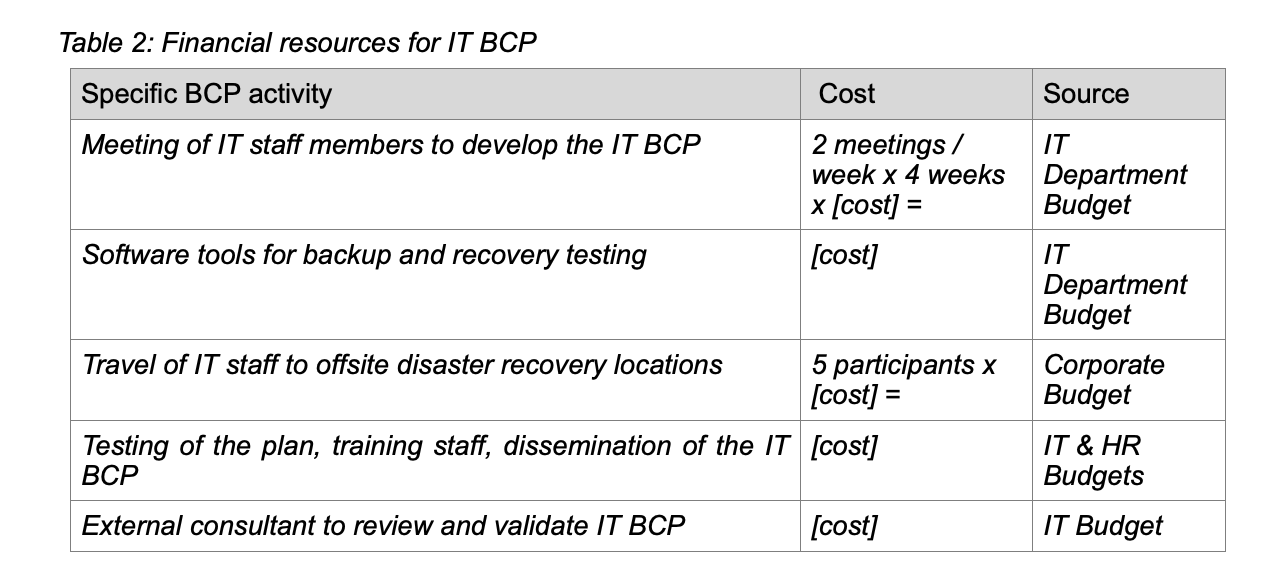
Financial Commitment:
Senior management supports the IT BCP process by ensuring the necessary financial resources are allocated. This includes direct funding and/or requiring contributions from various IT units and departments. The following table scopes out the anticipated actions and allied funds for the IT BCP effort.
Political and Human Commitment:
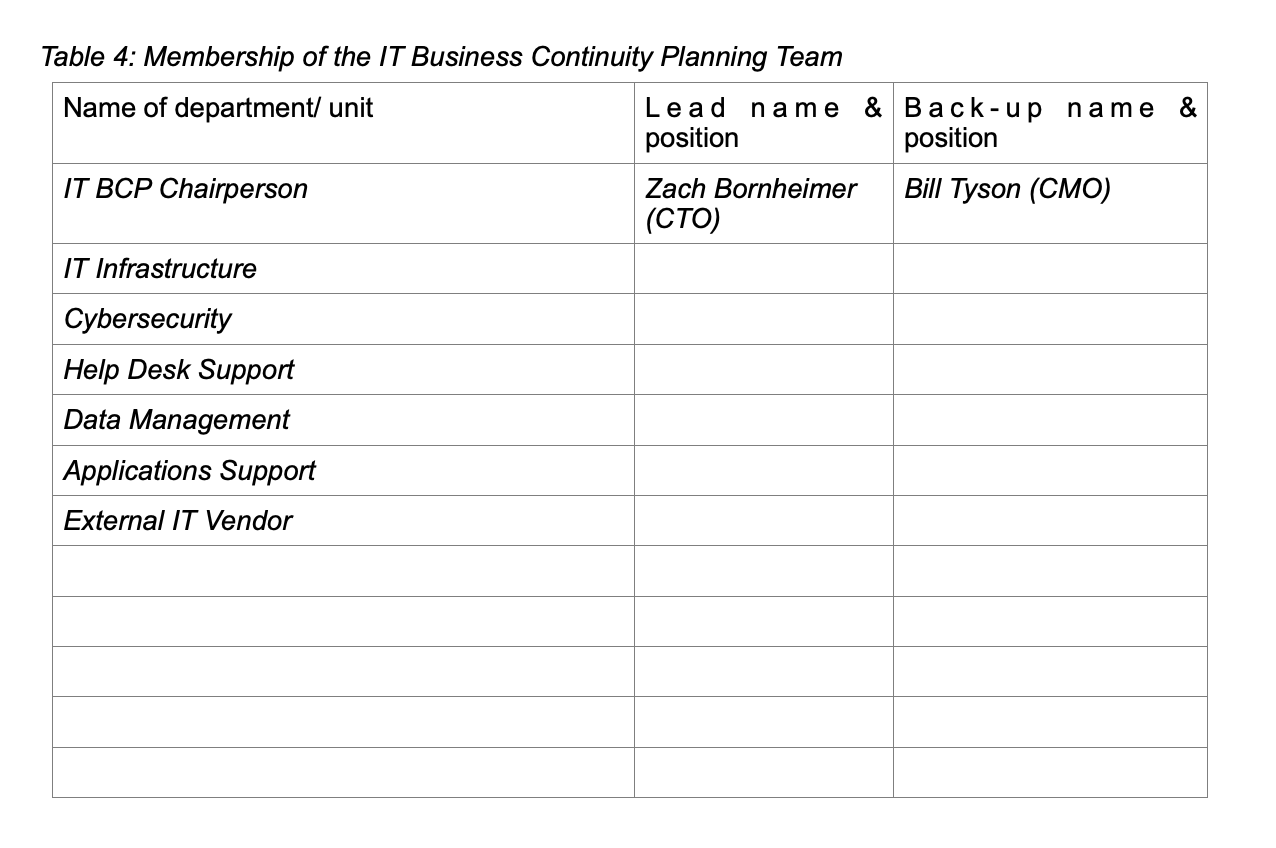
Senior management ensures the development of the necessary infrastructure and mechanisms for the IT Business Continuity Plan. This guarantees that all IT staff, from leadership to technical roles, understand the critical nature of the IT BCP and their involvement in it. The following table outlines roles and responsibilities across various IT departments.
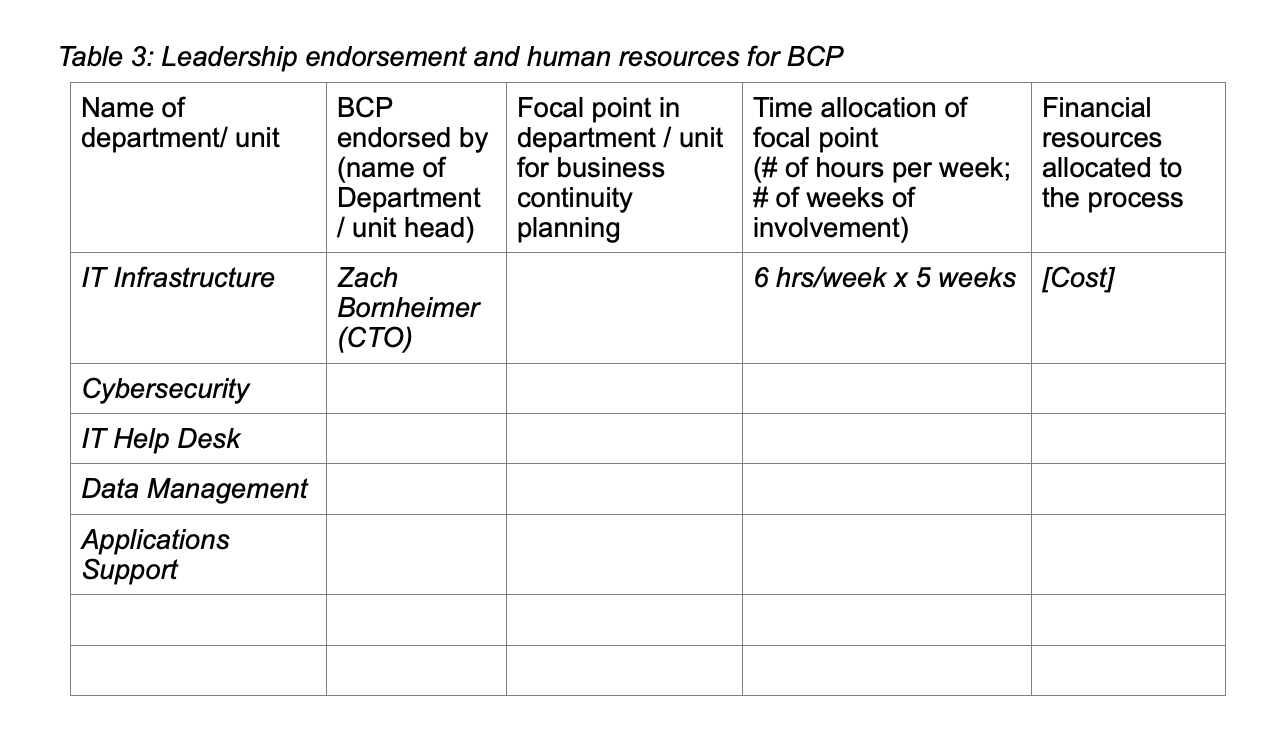
IT Business Continuity Planning Team:
The IT Business Continuity Planning Team is responsible for developing the IT BCP. The team includes IT managers, technical experts, and key representatives from essential IT functions. The team members are nominated by department heads and approved by senior management. The IT Business Continuity Planning Team Chairperson will be appointed by senior management.
5. Policy
5.1. The strategy of IIP’s business continuity plan
To develop, implement, and manage a robust and effective Business Continuity Plan (BCP) to protect IIP operations, including its customers, employees, contractors, sub-contractors, and interested third parties.
There are three primary aspects that IIP considers for its business continuity plan concerning key applications and processes:
High availability: Providing the capability and processes so that a business has access to web applications regardless of local failures. These failures might be in the business processes, physical facilities, or IT hardware or software.
Continuous operations: Safeguard the ability to keep things running during a disruption, as well as during planned outages such as scheduled backups, power outages, or planned maintenance.
Disaster recovery: Establishing a way to recover data processing facilities at a different site if a disaster destroys the primary site.
5.1.1. Plan Objectives
Serves as a guide for IIP and its recovery teams.
Reference any relevant data that resides outside this document.
Provide procedures and resources needed to assist in recovery.
Identify notification procedures in the event of a disaster.
Identify, assess, and minimize risks.
Assist in avoiding confusion experienced during a disaster by documenting, testing, and reviewing recovery procedures.
Document storage, safeguarding, and retrieval procedures for vital information and data.
The IT Security team has created a Business Continuity Plan in conjunction with the Disaster Recovery Committee. The Disaster Recovery Committee and Business Continuity Committee are responsible for maintaining the BCP.
The BCP will be implemented to maintain or restore critical operations within agreed timescales.
5.1.2. The BCP will include a reference to:
Critical IIP systems
Critical IIP employees and stakeholders
Business continuity roles and responsibilities
Performed risk assessments
Compliance with customers’ security requirements and contractual agreements;
Compliance with IIP information security management system (ISMS);
Operational procedures that will ensure recovery and restoration of business operations and availability of information within agreed timescales;
Education of relevant staff on pre-defined procedures;
Testing and updating of plans and procedures.
5.1.3. Identification and management of risks and Business Impact Analysis (BIA)
The IT Security team will perform annual risk assessments and Business Impact Analysis to identify issues that will affect the ability to provide services to its customers. Additional information relating to Business Continuity Planning (BCP) can be found within this document (section Scenarios section) and Business Impact Analysis results. Also, the set of important risk mitigation measures is highlighted in the section Risk Mitigation Measures.
5.1.3.1. Risk Mitigation Measures
This chapter delineates the proactive measures undertaken by IIP to identify, minimize the likelihood, and mitigate the potential impact of risks on our global business operations.
In response to the dynamic risks of today's landscape, we continuously refine our processes and bolster our business resilience.
Over the past two years, aligning with global events, we have adopted a strategy of global business diversification, resulting in the following key advantages:
Global Team Distribution:
IIP team is strategically distributed across various state locations:
100% in the US
Each team has representatives in different states to minimize location-specific risks.
Cloud-Based Infrastructure:
The entire infrastructure, including Infrastructure as a Service (IaaS) and Software as a Service (SaaS), is cloud-based, enhancing flexibility and resilience. No client data is stored or processed in internal DC. Customer data is processed or stored only in tenant in geo location of country to compliance with. E.g. Canadian customers have AWS instances in Canada.
Site-to-Site Virtual Private Networks (S2S VPN):
Secure and available S2S VPNs are established to facilitate remote work. 2FA is enabled on all client-side connections. PKI is in use for S2S with customers who have enabled these connections. Keys rotation is performed every 1Y.
Alternative Business Operation Locations:
We have created and maintained alternative locations in the USA to ensure continuity of business operations.
Uninterrupted Power and Energy Sources:
In the locations with some risk factors, we equipped the uninterrupted power sources, alternative energy supplies and fuel generators for electricity.
Redundant Communication Channels:
Each location is furnished with alternative communication sources (2 internet providers). In the locations with some risk factors, we equipped 3rd satellite internet channel based on Starlink.
Regular Training and Testing:
IIP conducts regular training sessions (annually) and tests for emergency situations and tools to minimize potential consequences.
Crisis Committee for each Risk factor:
A dedicated Crisis Committee is organized for each identified risk, equipped with detailed action plans for various scenarios.
Communication of BC/DR Plan:
The Business Continuity/Disaster Recovery (BC/DR) plan has been communicated to all employees, ensuring preparedness for emergency situations.
By implementing these comprehensive risk mitigation measures, IIP fortifies its global operations against potential disruptions, exemplifying a proactive approach.
Through effective implementation of measures, IIP has not yet experienced any business interruption incidents since its establishment.
5.2. Business Continuity and Disaster Recovery Needs
Our Business Continuity Strategies include:
Pre-Escalation:
Employee communication and training
Remote work policies and infrastructure
Data backup and cybersecurity measures
Insurance coverage review
Supply chain contingency plans
In Case of Escalation:
Evacuation procedures and safe havens
Shelter-in-place protocols and emergency supplies
Communication protocols and reporting mechanisms
Financial and mental health support for employees
Post-Escalation:
Damage assessment and recovery strategies
Employee wellbeing and support programs
Business resumption planning (remote work, relocation, office repairs)
5.3. Our BCP objectives:
There should be the capability to ensure Business Continuity for 72 hours following any Critical Situation.
The technical environment should be recovered within the specified timelines (up to 8h).
The business process should be fully recovered within specified timelines (up to 4h).
5.4. General Business Continuity Prerequisites
Internet access should be provided by several separate ISPs (at least two), with a main and a backup Internet connection. Failover and load balancing, with automated switching, should be available. IP addresses should be whitelisted on the customer side.
Encrypted Data backups should be stored off-site at AWS.
Key employees should have corporate laptops configured adequately with a sufficient level of security.
All employees should be able to work outside of the company office in case of a Critical Situation.
5.5. Disaster Recovery Activities
IIP employees and clients should be notified as soon as possible via email and phone call.
IIP employees and clients should be provided with periodic updates during the Critical Situation and its Recovery (performed via <Service Name>).
Notification should be done via an email message, following a phone call to appropriate stakeholders.
The Recovery efforts should be coordinated with the key stakeholders.
The most recent verified backup should be used to restore data and files.
The document Recovery efforts should be appropriate to the value of the losses.
The integrity of restoring systems and data should be verified before re-releasing into production.
All the other necessary Recovery activities should be taken according to the circumstances.
5.6. Disasters Scenarios & Risks
We have developed and implemented a Business Continuity Plan (BCP) for IIP where the most risky scenarios were taken into consideration in order to keep up and running our critical business processes, functions and activities.
5.6.1. Natural disaster (major fire, major flood, earthquake - regardless of source)
Upon discovery of a disaster, the following procedures should be followed:
Local HR or teams that are located in impacted geographic areas should immediately inform all employees and contractors of the danger.
Order everyone to leave the danger zone, Head of HR should and PM team coordinate employees to the safe location.
Local managers/employees should immediately report to local emergency services about the situation.
Employees/Contractors should leave the danger zone as soon as possible.
Employees/Contractors must assist other team members, customers, and guests during the evacuation.
If you are not near the workplace, it is forbidden to return to it and try to take away any material resources; everyone must immediately go to the safety zone.
If an employee or contractor is in the workplace near valuable resources, such as money, important documents, laptops, and others in his area of responsibility, he can take them out of the area of danger only if it does not require additional time, does not interfere with evacuation, and does not endanger people.
Project and team leaders need to make sure during the evacuation process that none of their teams remain in danger.
Provide the arriving rescue services with the necessary information about possible victims and people they cannot find.
Once people are safe, start implementing disaster recovery and business continuity plans.
Head of HR should take care of the employees affected and their families from the “emergency budget”.
Inform customers if the situation has affected them or could potentially affect them in the future, and indicate the approximate time of resumption of services.
5.6.2. Epidemic Health Situations
IIP will advise each contributor/employee/contractor to work from their homes to minimize the risk in case of epidemic health developments.
The additional measures to mitigate the issue are the following:
Follow the instructions of the World Health Organization (WHO) and other government institutions.
Disinfectants are installed along with a thermometer to check each person who enters any IIP facility.
Remote shifts are enforced. Full remote is initiated in case more than 6 people are impacted.
Office presence is analyzed to track infection chains.
Monitor the situation and government enforcement regarding the matter.
Head of HR is in charge of monitoring employees' health issues, helping them to recover quickly, guiding and consulting them and their relatives.
It is expected that in such a distributed environment, no more than 30% of staff should be impacted. Timing is everything.
Each employee/contractor with symptoms must inform their teammates, PM and Head of HR about the disease.
In case of a contagious infection, a quarantine is required, and the employee should be provided with all necessities to work remotely from home.
5.6.3. IT Incident (Data breach, Penetration, Ransomware, virus, equipment failure, communication, theft, robbery of work equipment)
In the event of loss of control over the workstation hardware because of, but not limited to, theft or virus infection, the following actions should be taken to ensure the safest path to resolve this incident.
IT Incident Response Team and employee Manager - must be informed immediately via email at IIP Emergency Support info@softwareautomationholdings.com.
The Incident Response Team investigates the situation and assigns a severity to the threat. IIP CISO, Tony Robinson and IR team would start investigation immediately.
Any credentials to the systems that could be stored on the workstation or mobile device must be revoked.
In the case of a virus infection, any infected device must be shut down as soon as possible. Employees who were impacted should take additional training on KnowBe4 platform. Manager should be notified. SOC validates if this is part of targeted campaign or accidental
Impact assessment should be done by IIP CISO, Tony Robinson.
Until the Incident Response Team clears a device following a reported incident, its use is prohibited.
Analysis of the causes and consequences of the incident, implementation of changes, and training of employees.
Detailed information on the management of security incidents involving IIP and its clients' information and information technology resources can be found in the IIP Incident Response Plan.
Activate our Professional Liability & Cyber Insurance by Chaucer Insurance Company;
Cyber incident helpline: 201.847.9175; Customer Number 0010284
5.6.4. IT Incident (Network outage, Power outage)
5.6.4.1. Unavailability of Primary Internet Provider
In this scenario, if the primary internet provider becomes unavailable, an automatic switch to the secondary network provider is configured (failover). No delays are expected, and there is no need for additional communication regarding this incident with the Asset Manager.
5.6.4.2. Unavailability of Both Network Providers
If both network providers are unable to provide their services, any employee/contractor who discovers this issue must notify the Asset Manager immediately. If the Asset Manager is unavailable, the Chief Operating Officer (COO) should be notified. This notification should be made through any accessible means, such as a phone call, internet call, message on instant messengers (e.g., Google Chat, Slack), or email.
The local IT administrator is responsible for activating and enabling employees to connect the 3rd alternative internet channel and involving anyone necessary to address this task, guiding the team.
Upon connection is established and the local team is back online - notification to BCDR committee should be done via email with details about the incident and recovery time. In the following emails, IT should also provide lessons learned and proposals for improvement if the recovery wasn’t smooth.
5.6.4.3. Unavailability of Central Power Supply
In the event of an unanticipated central power supply outage, the main fuel generator automatically starts supplying power to the local office.
If the main generator is not working, the following steps should be taken:
Notification: Any employee or contractor who identifies the central power supply issue must promptly inform the Asset Manager. If the Asset Manager is unavailable, immediate notification should be directed to the Chief Operating Officer (COO).
Power Restoration: The Asset Manager is responsible for initiating power restoration by activating the generator. This process should be executed in accordance with the instructions outlined in the "How to Turn On Electricity (From the Generator)" manual.
Maintenance Coordination: To ensure timely maintenance, the Asset Manager is required to communicate the generator start time to the office support team.
In the event that the central power supply is restored, the subsequent steps are as follows:
Generator Deactivation: Upon confirmation of central power supply recovery, the Asset Manager should follow the prescribed steps detailed in the "How to Switch from a Generator to Power from the City Network" manual to deactivate the generator.
Maintenance Notification: Similar to generator activation, the Asset Manager must inform the office support team about the generator deactivation time for maintenance scheduling.
By adhering to these procedures, the continuity of power supply can be effectively managed during periods of central power supply unavailability.
In the event that centralized power supply is not restored within 24 hours, we anticipate relocating teams to pre-arranged alternative locations where both centralized power supply and communication are ensured, as well as locations equipped with backup power systems and internet connectivity.
5.6.5. Terrorism attack or Increased military aggression
Possible Scenarios:
Missile Attacks: Sudden, high-impact events causing casualties and infrastructure damage.
Ground Engagement: Prolonged conflict with potential for collateral damage and movement restrictions.
Cyberattacks: Disruption of critical infrastructure and data breaches.
Civil Unrest: Protests, demonstrations, and potential violence.
Only two main requirements are needed for the continuous provision of services to our customers: stable access to the Internet and employees hosted in a safe place.
5.6.5.1. Technical preparedness
IIP uses a cloud-based approach to keep up and running services and processes needed for software development and internal operations of a company. No customer data is stored or processed in Ukraine or any other country with high or critical risk.
Most of the engineering and delivery team (100%) is diversified and located in the USA.
Any office separately doesn’t impact the situation, as we host all data in the AWS Cloud or other cloud solutions and don’t store or process any customer data locally.
All the company’s cloud-hosted resources are available via secure, encrypted VPN tunnels.
The redundant VPN connections are built using at least two ISP providers and an Internal BGP routing protocol between the diversified delivery locations and AWS IIP account (or other cloud) to grant secure encrypted access via VPN Site-to-Site tunnels. Access to internal company resources is also available through corporate SSL VPN connections.
5.6.5.2. Organizational preparedness
All employees and contractors can work effectively from home or any other location. After COVID-19 IIP is a REMOTE-FIRST company.
We prepared detailed instructions for employees and contractors, considering factors that depend on the scale and impact of this issue, and, of course, on the restrictions/instructions that can be applied by the government.
On the other hand, IIP is committed to helping employees/contractors and their families in case of dangerous scenarios like this.
We continuously monitor the situation and notify our stakeholders and customers of any major events or changes in situations or risk escalations.
A crisis communication plan and list of responsibilities will be provided in case of this scenario.
The plans of action for every team are described within the Business Impact Analysis results.
5.6.5.3. Crisis communication plan and responsibilities for scenario Man-made disaster
In case of receiving information about any type of man-made disaster, including radiation leakage/accident at a nuclear power plant, the engineer is obliged to immediately notify his PM by phone, the CEO by e-mail, and Incident Commander by phone (backup channel - corporate mail or chat.)
The CEO will notify all members of the Crisis Management Team about the occurrence of a dangerous event according to the contact table. The Crisis Management Team should perform further actions according to this plan.
Incident Commander sends out email communication templates to all employees stating they will receive instructions over the next few hours. It can be duplicated in all Communication channels, Slack, email, etc.
Crisis Management Team members should get in contact immediately via online conference meetings, phone calls, and messenger applications to analyze the information and select a scenario according to the situation. The meeting is organized and managed by the Incident Commander.
Incident Commander takes control of all other involved Teams' actions and launches approved response scenarios with clear instructions on the initial actions.
The HR Team keeps track of all contractors that might be affected, making sure everyone receives the instructions and understands what needs to be done in the course of this disaster. Updates Crisis Management Team on the overall situation every two hours. Creates the list of those immediately affected by disaster, potentially affected by disaster, and not affected.
PMs and Team Leads additionally communicate with all members of their teams to confirm their receipt of the action plan, verify their availability, limitations, and readiness to follow the plan. Tasks and duties are distributed among those employees who are not affected by the disaster.
The COO is preparing to use funding reserves to cover urgent expenses.
Crisis Management Team appoints responsible persons (Monitoring Team) for continuous monitoring of available information on current changes of the situation.
Risk Monitoring Team submits a report on the current situation at least three times per day or immediately upon receiving an important update.
IT Recovery Team tests the availability of the primary and backup communication channels to provide continuous customer service.
Pre-relocated team (Remote Team) takes responsibility for the provision of critical services to customers and communication with clients (if necessary)
The Marketing Team and Sales Team inform the company's customers about the current situation, possible risks, and restrictions in providing services, and approximate recovery time, according to the prepared communication map and the current situation. Keeps in touch with customers, continuously informs them about changes in the situation.
Crisis Management Team is responsible for:
Analysis of the need to protect contractors and their families and the procedure for providing such assistance.
Re-establishing communication with out-of-contact contractors.
Analysis of available options for transporting people, if necessary.
Assist the families of contractors in ensuring their safety and allocating the necessary resources.
Assess the existence of restrictions on crossing the borders of countries planned for relocation.
Drawing up relocation plans for groups of contractors and family members, and appointing the leader of each group.
Organization of the teams' work that remains at the primary location, if available.
Coordination of the work of all other teams, change of action plans according to the development of the situation.
15. The Finance Team, if necessary and agreed, is responsible for:
Providing the necessary financial resources to other teams to carry out their tasks
Providing financial assistance to contractors and their families as needed
Organization of alternative payment options for contractors
Monthly cash payment in the amount of the monthly compensation to the families of contractors involved
16. HR Team is responsible for:
Preparing contacts with contractors and their families, liaising with them, and identifying needs that the business can help with
Organization of purchase and lease of necessary resources (tickets, documents, vehicles, fuel, food, water, communications, maps, and schedule, etc.)
Assistance in solving current problems during a crisis or business trip
5.7. Testing of the Business Continuity Plan
The reason for testing the Business Continuity Plan is to simulate situations to find out the gaps during real problems.
The Business Continuity Plan (BCP) is tested once a year - but can occur more frequently in the case of significant changes.
Once the exercising and testing are performed, the person who coordinates business continuity reviews the results, compares them with the objectives set, and reports them to top management.
5.8. Communication Channels
The primary corporate communication channel for calls and chats is email, Slack, etc.
The alternative to communication is by telephone. For Critical and high-severity incidents, phone is the primary communication channel.
For any crisis event, as described throughout this continuity plan, the following order of communication should be applied:
Make a call and key stakeholder notification for any critical or high-severity events.
Inform all team members of the situation and advise on actions.
Use email to duplicate communication messages.
HR Manager is assigned the role of Incident Commander and coordinates point-to-point communication across the management team.
The “I’m-ok” procedure is established in case of significant disaster situations, such as natural disasters. Each team member informs their manager regarding their whereabouts and well-being.
The company’s Team List is used to mark off safe team members.
6. Disciplinary Action
Employees who violate this policy may face disciplinary consequences in proportion to their violation. Management will determine how severe an employee’s offense is and take the appropriate action.
7. Change, Review, and Update
This policy shall be reviewed once every year unless the owner considers an earlier review necessary to ensure that the policy remains current. Changes to this policy shall be exclusively performed by the Information Security Manager and approved by the IT Committee and CEO.
